
Seed Phrase Crypto Wallet Security Risk Mitigated 2026 | Scroll Wallet
Blockchain wallet recovery is the process of restoring access to your existing digital assets on the ledger using cryptographic backups, rather than resetting ownership or changing passwords on a centralized server. Since self-custody means you hold the only keys, losing your device or app requires using a seed phrase or social recovery guardians to reconnect your identity to your funds. We design these systems to ensure that even if your hardware fails, your ownership remains absolute and verifiable.
Losing access to a crypto wallet is one of the most painful things about self-custody, and it almost always happens for the same reasons. The phone was stolen. The laptop is broken. I did a factory reset and only then remembered about the wallet. I forgot my PIN, which seemed so obvious six months ago. The root of all these stories is the same: the access data was stored in such a way that the first failure destroyed it. Understanding exactly how this happens means doing half the work of protection.
The most common scenario is the loss or breakdown of the device. The phone is broken, stolen, or simply refuses to turn on. An extension in a browser on a laptop that burned down - the same story. The wallet itself has not gone away: it exists in the blockchain, the money has not been burned. But without a seed phrase or private key stored separately from the device, it is impossible to restore access. This is not a blockchain bug. This is a direct consequence of self-storage - you keep the keys, and no third party can reset your password.
The second most common case is accidental deletion. The user clears the memory, reinstalls the system, or switches to a new phone, sincerely not understanding that the wallet does not synchronize with the cloud like a regular messenger. Recovery after deleting an application is possible only under one condition: the seed phrase is recorded and stored offline. Without it, reinstallation gives a clean, empty wallet - not yours. The third scenario is a forgotten local password or PIN. Many wallets add a local authentication layer on top of the seed phrase. Forgot your PIN and didn't write down the seed phrase separately? All. The application will not save you - there is no way back through it.
There is another problem - less obvious, but increasingly common. Confusion due to old or multiple wallets. Those who have been in crypto for several years have often created two or three wallets at different times, on different devices, with different seed phrases. When trying to restore access, they enter the wrong phrase, receive the wrong wallet, and decide that the funds are missing. Although in fact the money is simply lying at another address, which they no longer recognize. Scroll Wallet was created precisely to ensure that the connection between your seed phrase, address and activity in the blockchain is absolutely transparent - you always know exactly which wallet you are working with and what it controls.
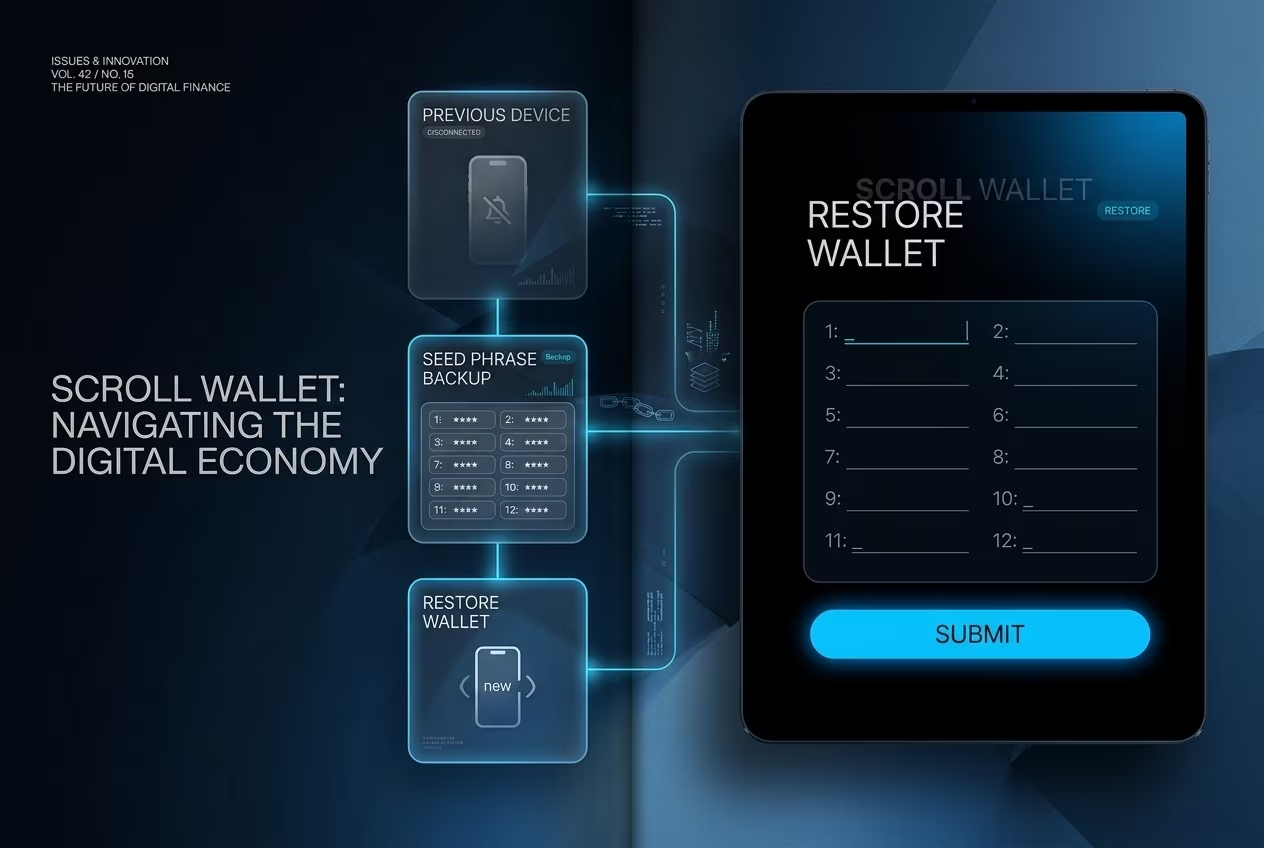
Losing access to your device does not mean losing your assets, provided you have maintained your recovery credentials. Follow these steps to restore your Scroll Wallet on a new device or after a fresh application install.
Recovery depends on what was lost and what backup material still exists. The table keeps the distinction clear: device loss is usually recoverable, key loss often is not, and partial information belongs in a specialist-risk category.
| Scenario | Recoverable | Requirement |
|---|---|---|
| Lost physical device | Yes | Restore the complete seed phrase or hardware-wallet backup on a new trusted device. |
| Deleted wallet app | Yes | Reinstall the verified app and import the original phrase instead of creating a new wallet. |
| Forgotten local password | Usually | Reset the local vault and recover with the seed phrase; the password itself is not the on-chain key. |
| Damaged hardware wallet | Yes | Use the recovery phrase with a replacement hardware wallet from a verified vendor. |
| Partial seed phrase | Conditional | Specialist recovery may help only when enough words, order, and wallet context are known. |
| Stolen device | Yes, but urgent | Restore from backup, then move funds to a fresh wallet if the old device could expose credentials. |
| Lost seed phrase and no active wallet | No | There is no technical way to reconstruct the private key from public blockchain data. |
Source data: CoinBureau guide covering common crypto wallet recovery scenarios.
In a non-custodial wallet, the recovery phrase is not just “backup”. This is your wallet. When creating a Scroll Wallet, the system generates a seed phrase of 12 or 24 words according to the BIP39 standard. This sequence is the human-readable form of your private keys, cryptographic credentials that prove ownership of assets on the network. This information is not stored anywhere else. Not on our servers. Not our team. Nowhere.
Recovery is a completely local process. When you enter a 12 or 24 word phrase on a new device, the BIP39 algorithm deterministically recreates the same private keys and wallet addresses that were originally created. No network requests. No account search on our side. Mathematics produces the same result every time with the same input - that is why the phrase must be kept secret and stored offline. Experts Ledger Academy confirm: the seed phrase is the only backup copy of your private keys. The only way to restore access without the original device and without the participation of any providers.
Scroll Wallet encrypts keys locally on the device - via a password or PIN. This is real protection: it does not allow access to the wallet if the device is physically stolen. But it does not replace the seed phrase. Lost your device and forgot your PIN? Local encryption does not provide any path to recovery. The phrase of restoration remains the only point of truth. This is not a flaw in the architecture; it is self-storage architecture. Full control means full responsibility.
So let's be clear: we can't reset your access. No support ticket. No identity verification. No backend override to recover a lost wallet. Providers in a non-custodial model do not store keys - intentionally. If you lose a 12 or 24 word phrase and there is no backup, the funds will be unavailable forever. Getting to the bottom of this before restoration is needed is the only sensible approach. Write the phrase down when you set it up, store it in at least two different physical locations, and treat it with the same seriousness as the assets it protects.
When you attempt to recover access to an old crypto wallet, understanding the financial landscape is your first line of defense. Legitimate recovery infrastructure operates on transparency and verifiable results, whereas fraudulent actors rely on psychological pressure and upfront demands. We have outlined the standard cost models and red flags to help you distinguish professional assistance from common exploits.
| Service Category | Typical Cost | Payment Model & Indicators |
|---|---|---|
| Legitimate Recovery (e.g., ReWallet, KeychainX) | 10% - 30% of funds | Success-based pricing. No upfront fees; payment is taken only after successful recovery. |
| Recovery Scams | $500 - $2,000 | Red Flag: Demands advance payment, private keys, or seed phrases without proof of work. |
| Hardware Replacement | $100 - $300 | Fixed cost for new Ledger or Trezor devices to restore a backup. |
| Forensic Tracing | Contingency-based | Often performed on a conditional basis depending on the complexity of the blockchain trail. |
| Network Gas Fees | Variable | Standard blockchain transaction costs required to move recovered assets to a new secure address. |
Wallet recovery should be a deliberate, structured process you control - not an emergency you barely survive. Web3 infrastructure experts are converging on one uncomfortable truth: recovery best practices have to stop being panic-driven workarounds and start being designed capabilities. Built in. From day one. Recovery isn't a last resort. It's a feature - and if you're treating it as anything less, you're already behind.
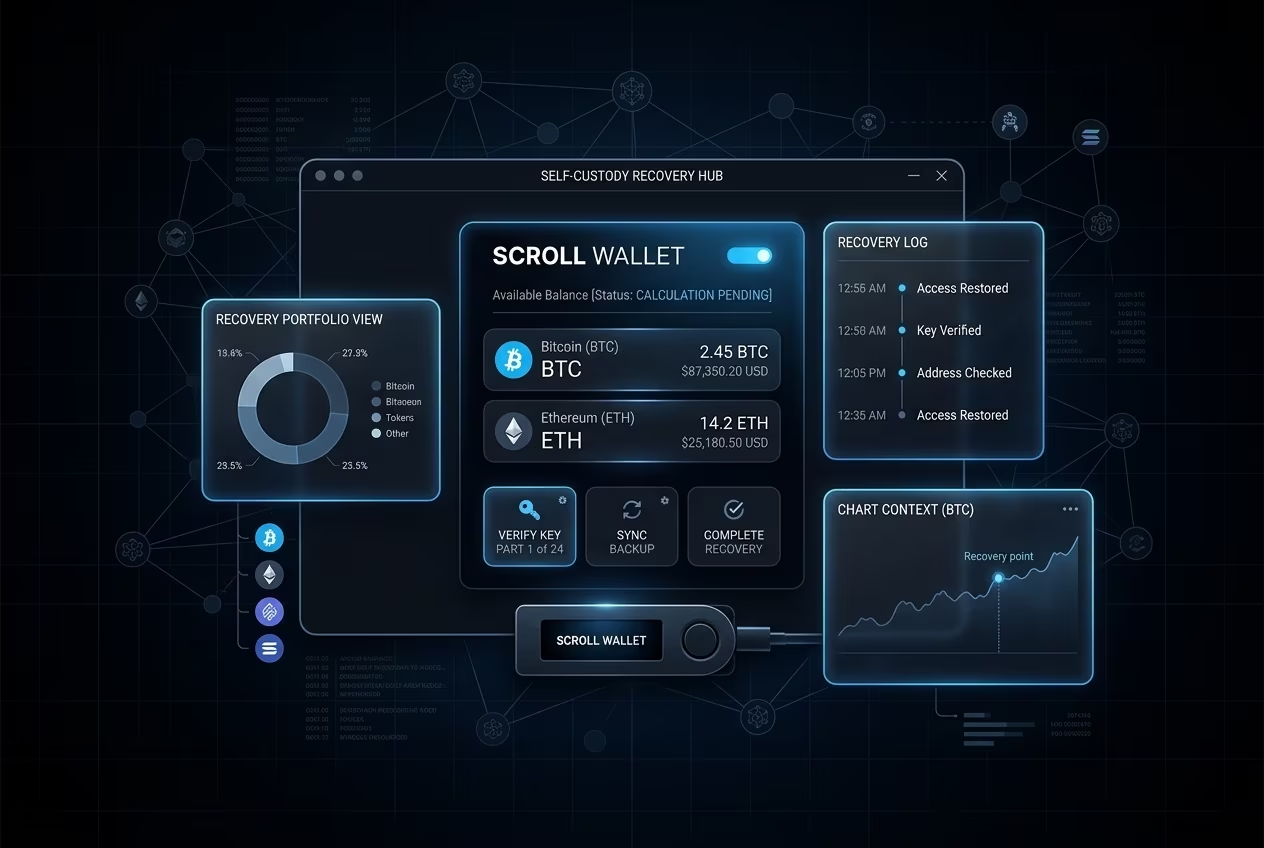
User-controlled wallet recovery demands clean separation between access layers. Your seed phrase, your device authentication, your recovery contacts or shards - each plays a distinct role. Conflate them, store them together, and a single point of failure becomes a total loss. Scroll Wallet's architecture treats recovery as a first-class feature: the paths back to your wallet are defined before you ever need them, not improvised at 2 AM under pressure when something has already gone wrong.
Full self-custody control is the standard serious teams are pushing toward in 2026 - and the pressure is real. Multi-chain environments and L2 fragmentation have made wallet management genuinely complex. Holding assets across multiple networks means a recovery failure on one chain can cascade into access problems everywhere else. The expectation from infrastructure teams worth listening to: recovery flows must be chain-aware, verifiable, and transparent. You should be able to confirm your recovery setup is intact without calling anyone, trusting anyone, or hoping anyone picks up.
Here's the blunt expert consensus: recovery readiness is a measurable state, not a feeling. You either have a tested, documented recovery path - or you don't. No middle ground. Scroll Wallet makes that state visible and actionable: verify your setup, update it when your life changes, execute recovery without external dependencies. The goal isn't to make recovery easy in ways that gut your security. It's to make it structured enough that uncertainty - that low-grade dread of "what if" - simply stops being part of the equation.
Wallet recovery is no longer reliant on a single seed - the industry is moving to distributed architectures where there is no single point of failure costing users billions. The classic sequence of 12 or 24 words carries with it a harsh mathematical reality: the loss of five words reduces the probability of recovery to almost zero, and one theft means a complete, irreversible loss of everything. This is not a problem of inattentive users. This is a structural defect in the design itself. The industry has recognized this, and a shift is already underway in three converging directions: account abstraction, social restoration, and multi-key schemes.
Account abstraction, standardized through ERC-4337, breaks the rigid “one private key - full control” model and replaces it with programmable wallet logic. Recovery rules are written directly in the smart contract code: time locks, custodian approvals, spending limits, backup mechanisms - everything becomes configurable parameters.Social recovery goes further: trusted contacts vote to restore access collectively, no custodian can act alone, and no point of compromise will empty the wallet.Multi-key wallets based on m-of-n threshold schemes, they distribute signing rights between several devices or participants - the attacker will have to simultaneously hack several independent systems. The task becomes dramatically more difficult. According to Phemex, the new prototype already allows you to restore a wallet without revealing the seed phrase - through a mathematical proof of ownership that is generated in approximately 55 seconds and verified in less than 2 seconds. Specific signal: cryptographic recovery without data disclosure is ready for production.
In addition to threshold schemes and social recovery, hardware-secured storage through Trusted Execution Environments - such as Intel SGX - opens up a self-storage model using cloud enclaves. Key material never leaves the verified secure enclave, and biometric authentication blocks access at the hardware level, not the application level. Even a completely compromised operating system will not be able to extract credentials. Combination of TEE key storage, biometric binding and recovery logic on the blockchain via account abstraction creates a layered defense where no single failure - lost device, stolen password, compromised custodian - results in a complete loss. Each layer independently increases the cost and complexity of the attack.
In Scroll Wallet, recovery architecture is a first-level decision, not something that is thought about at the end. The practical takeaway is simple: the question is no longer whether to move away from the seed, but rather what combination of recovery mechanisms fits your threat model and usage pattern. A technically confident user working alone can opt for a 2-of-3 scheme on personal devices. Less technical - will benefit from social restoration with set guardians and a time-lock in case of an emergency. The main thing is that the architecture distributes control, removes single points of failure, and the recovery logic remains transparent and verifiable. No proprietary black boxes. This is the standard we are moving towards.
Scroll Wallet is created for those who perceive access restoration and self-storage of assets not as a bonus, but as a basic requirement - without compromise. In 2026, the cost of a failed recovery or an incorrectly saved seed phrase is not an inconvenience. This is a permanent loss of assets. Scroll Wallet's self-storage architecture is built around this reality: private keys never leave your device, and the recovery process follows clear steps that are documented, verifiable and reproducible long before they are needed in a critical situation.
Most wallets do not break during an attack. They break during restoration. Users discover that the backup is incomplete, the phrase was saved with an error, or the recovery interface behaves differently than expected - under pressure, under stress, when there is no time. Scroll Wallet solves this problem at its root: backup verification is built into the wallet creation process as a required step, rather than as a pop-up window that can be ignored. You confirm that the recovery phrase works before the wallet is considered active. This one solution eliminates the most common cause of loss of funds in self-custody: a broken backup that is discovered too late.
Self-storage in a multi-chain environment is a different level of complexity. L2 fragmentation, bridge interactions, assets distributed across dozens of networks - a wallet that protects only one chain creates blind spots. Self-custody in Scroll Wallet covers the entire Scroll L2 ecosystem with a single key management logic: the same recovery credentials cover your entire on-chain footprint within the network. No separate seed phrases for each chain. No parallel backup systems. The security model remains simple enough to actually be followed - not just declared.
Clear recovery steps are most important precisely when the conditions are at their worst: device failure, account blocking, severe time pressure. Scroll Wallet structures recovery documentation as a sequential, verifiable process—each step produces a verifiable result before you move on to the next. You don't have to believe that everything worked. You can check it out. There is a fundamental product decision behind this: transparency in the operation of the recovery mechanism is not an element of UX design. This is a security property. A user who understands exactly what their recovery phrase controls, where it applies, and what it cannot do is incomparably more resistant to phishing and social engineering - the two main attack vectors for self-custody in 2026.
Your ability to regain access to a crypto wallet is decided entirely by choices you made before anything broke - not in the panicked moment after. Recovery doesn't activate on demand like some emergency feature. It's the direct result of deliberate preparation: your seed phrase written down and locked away offline, a clear understanding of your wallet's architecture, and an honest answer to the question - do you actually know where your backup is right now?
The process to restore a wallet from backup works exactly as it should, but only when the backup itself is complete and reachable. A 12- or 24-word seed phrase, kept offline and never once touched by a network-connected device, is the single most valuable thing in your entire self-custody setup. Full stop. Scroll Wallet is built around this reality: when your seed phrase is intact, the recovery flow is clean, guided, and unambiguous. But no wallet software - ours included - can reconstruct access from nothing. Lost backup? Corrupted phrase? Never created one? Then the path back to your funds gets brutally narrow, fast.
Safe recovery also means controlling the environment you're acting in. Phishing sites, fake recovery tools, and social engineering attacks don't target random users - they specifically hunt people already in a stressed, desperate recovery situation. These threats in 2026 are sharper and more targeted than most people expect. So: always verify the source of any recovery interface. Use only official Scroll Wallet channels. And never - under any circumstances - enter your seed phrase into a form you didn't open directly from a verified application or URL. Not optional precautions. The absolute baseline for any recovery attempt that doesn't end in a second, worse loss.
Scroll Wallet is built to cut through the complexity of multi-chain environments, reduce fragmentation across L2 networks, and give you a clear, verifiable path through every critical action - recovery included. The architecture reflects one core conviction: clarity and preparation are the only real security guarantees in self-custody. Everything else is noise. Review your backup today. Confirm your seed phrase is stored correctly. And treat recovery readiness as an ongoing part of how you manage your assets - not a task you'll get to when something finally goes wrong.