Anonymous Crypto Wallet Reddit: Privacy Solution 2026 | Scroll Wallet

To receive money online anonymously, you must utilize non-custodial wallets and zero-knowledge proofs to decouple your identity from the transaction. Traditional payment apps track your metadata and link every transfer to your real-world profile. By switching to decentralized infrastructure like Scroll Wallet, you can accept funds through ephemeral addresses that maintain your transactional privacy and security.
Every transaction you make online builds a surveillance profile — and most people have no idea how deep that rabbit hole goes. When you send or receive money through a digital payment platform, the system isn't just logging an amount and a destination. It's capturing device identifiers, geolocation data, transaction velocity, behavioral biometrics, full customer journey maps — all processed in milliseconds by machine learning models built for fraud detection, analytics, and routing. Not a side effect. The architecture itself.
And this stopped being a niche concern a long time ago. By 2025–2026, payment tracking had climbed to the level of formal regulatory attention in the United States. The Consumer Financial Protection Bureau (CFPB) opened public inquiry into digital payment privacy and consumer protections — an explicit acknowledgment that data surveillance through payment infrastructure is a systemic risk, not a thought experiment. Regulators are finally catching up to what privacy researchers have known for years: the metadata layer of a financial transaction carries real, personal exposure for ordinary users.
The practical consequence? Every time you use a conventional payment platform, you generate a detailed behavioral profile that can be shared across connected systems, sold to third parties, or exposed in a breach. Protecting your financial privacy online isn't paranoia. It's a rational response to documented, deliberate data practices. Traditional payment rails were never designed with user privacy as a priority — they were designed for compliance, fraud prevention, and monetization of transaction data. Privacy, where it exists at all, is purely incidental.
That's the gap. Scroll Wallet addresses it at the architecture level — giving you actual control over what data gets exposed and to whom, rather than leaving you dependent on platform policies that can be quietly rewritten overnight. Understanding why payment privacy matters is step one. Choosing tools that treat privacy as a hard design constraint — not a marketing bullet point — is step two.
When you receive money online, the level of privacy you maintain depends entirely on the infrastructure of the payment provider. Traditional systems and centralized apps often require full identity verification (KYC) and log extensive metadata, creating a permanent digital trail. For those seeking higher privacy control, a self custody wallet within the Scroll Wallet ecosystem offers a decentralized alternative by minimizing metadata collection and removing the need for central logging.
| Payment Method | Identity Exposure | Metadata Collection | Typical Fees | Privacy Level |
|---|---|---|---|---|
| Credit Cards | Full (KYC) | High (Processors) | 2% – 3% | Low |
| Digital Wallets (PayPal/Venmo) | Full (KYC + Social) | Extensive (Centralized) | 2.9% + | Low |
| ACH Transfers | Bank Details | Moderate | 0.5% – 1% | Medium |
| Decentralized (Scroll Wallet) | Wallet Address | Minimal (On-chain) | Network Gas | High |
Anonymous payment limits in the USA aren't accidental quirks — they're load-bearing walls, engineered into every regulated payment rail from the ground up. Federal law forces financial institutions to collect and verify identity before touching transactions above specific thresholds. Under the Bank Secrecy Act, any cash transaction clearing $10,000 triggers mandatory Currency Transaction Reports. Electronic transfers routed through banks, payment processors, or card networks fall under the Electronic Fund Transfer Act — a framework that ties consumer protections directly to identifiable accounts. The logic is brutal and simple: the moment you want legal recourse, you need a verified identity on the transaction.
Tighten the lens to the product level and the picture gets worse. Prepaid debit cards sold without registration cap reloads at $1,000 per day and total balances at $2,000 in most states. Peer-to-peer platforms trigger identity verification once cumulative annual payments cross $600, following updated IRS 1099-K reporting rules that reshaped the landscape in recent tax years. As Consumer Compliance Outlook points out, regulated payment rails are built around identifiable accounts precisely because consumer protection frameworks collapse without a traceable party. Privacy and regulatory coverage are in direct tension — not by accident, but by architecture.
On-chain environments swap one set of constraints for another. Public blockchains record every transaction permanently and pseudonymously — not anonymously. That distinction matters enormously. Blockchain analytics firms routinely cluster wallet addresses to real-world identities using exchange KYC data, IP logs, and on-chain behavior patterns. This analysis has gotten faster and sharper, making the assumption of on-chain anonymity increasingly unreliable for anyone transacting through centralized entry or exit points. The hard truth? The same anonymous payment limits that govern fiat rails follow you into crypto the moment you touch a regulated exchange or custodial service. Our ZK rollup privacy guide maps exactly where these exposure points occur and how zero-knowledge proofs shift the calculus for users who need verifiable privacy without sacrificing on-chain functionality.
Scroll Wallet runs on Scroll's ZK rollup infrastructure — transactions verified cryptographically, without broadcasting the full data set to every public observer on the network. This doesn't dissolve compliance obligations. It repositions where and how privacy gets preserved within them. Convert between fiat and crypto and you're back inside a regulated ecosystem. But at the on-chain layer, Scroll's architecture hands you meaningful control over what's visible and to whom — no obscurity tricks, no workarounds that crumble under scrutiny. Knowing exactly where anonymous payment limits hit their ceiling is the only honest starting point for figuring out where real, technically defensible privacy actually begins.
Your identity leaks before you ever hit "send" — and most people have no idea how many layers are already watching. The moment you connect to a standard payment platform, your IP address is logged, your device fingerprint is captured, and your linked card or bank account stitches the whole thing to a verified, real-world identity. Not hypothetically. Not in some future surveillance state. Right now, in 2026, this is just how payment processors work.
And it goes much deeper than your account details. The Consumer Financial Protection Bureau (CFPB) has flagged exactly this in its inquiry into digital payment privacy — platforms routinely harvest behavioral data, device identifiers, and session metadata that stretch far beyond anything you consciously handed over. Your transaction history, geolocation signals, session timing, browsing patterns — all of it stored, analyzed, and in some cases sold. No clear disclosure. No opt-out prompt at checkout. To actually reduce payment data exposure, you have to reckon with an uncomfortable truth: the risk isn't just in the payment. It lives in every data point attached to the session around it.
Then there's the compounding problem of platform records. Centralized services build internal logs that fuse your wallet address, email, phone number, and payment method into a single identity profile. Use a pseudonymous address? Doesn't matter. One linked card, one KYC verification — and that address is permanently anchored to your real identity in their database. Forever. Breaches then transform these internal records into public liabilities, and payment platforms have hemorrhaged hundreds of millions of records over the past few years alone. The real question isn't whether a platform you've used has been breached. It's whether your data was in the batch that walked out the door. For a structured look at the architectural decisions that actually move the needle here, the privacy wallet guide breaks down where exposure is built in — and where it can be cut.
Scroll Wallet was designed around this exact threat model. No linked cards required. No centralized identity verification to operate on the Scroll L2 network. Your on-chain activity stays inside a self-custody environment where device IDs and IP logs are not tied to a persistent user profile on our end. That said — and this matters — no wallet kills every exposure vector. Your network provider still sees your IP. Every bridge or external service you touch runs under its own data policies. The goal isn't zero exposure. That's a fantasy. The goal is meaningfully reduced payment data exposure through deliberate architectural choices. Knowing exactly where the leaks are is the only way to start controlling them.
Zero-knowledge proofs let you prove a transaction is valid while revealing absolutely nothing — no amounts, no addresses, no history, nothing. A prover generates a tight cryptographic proof that says "all conditions are met," and a verifier checks it cold, never touching the private data underneath. That's not a feature. That's a structural guarantee — and it's what separates real digital wallet privacy from a marketing slide.
The implications cut deeper than simple transfers. ZKPs can confirm a sender holds sufficient funds, that a transaction clears compliance thresholds, or that no suspicious pattern exists — all without storing or transmitting a single piece of personally identifiable information. As the team at 0xProcessing lays out in detail, ZKPs let payment gateways verify limits and transaction history without ever touching financial specifics — which satisfies GDPR, CCPA, and AML requirements without building a PII database in the first place. For you, practically speaking, your receiving workflow can be fully auditable by a counterparty or compliance layer while staying completely opaque to everyone else on the network. Auditable and private. At the same time.
ZK rollups push this logic into throughput territory. Batch dozens of off-chain transactions together, submit one compact proof to the main chain, and individual transaction details disappear into the aggregate — while the whole batch stays verifiable and final. This isn't a privacy-versus-scalability trade-off. It's both, simultaneously, by design. Scroll Wallet is built directly on this infrastructure, which is why non custodial wallet growth on ZK-based L2 networks keeps accelerating — users are finally realizing privacy and performance stopped being enemies. Every transaction through Scroll's ZK layer hits the chain as a verified proof only. Amounts and identities stay off-chain. Inaccessible. Full stop.
For anyone serious about building a private receiving workflow, the decisive advantage of an anonymous digital wallet backed by ZK infrastructure is simple: privacy gets enforced at the protocol level, not by trusting a company's privacy policy or hoping a developer made good choices. You don't need to trust anyone to protect your data — the cryptographic structure makes exposure architecturally impossible without your key. That said, ZKPs aren't a magic shield. Front-end phishing, compromised devices, and bridge vulnerabilities are still very real attack surfaces. Scroll Wallet addresses these at both the UX and architecture layers — but the strongest privacy posture always pairs ZK-native infrastructure with disciplined self-custody on your end. The protocol holds its side. You have to hold yours.
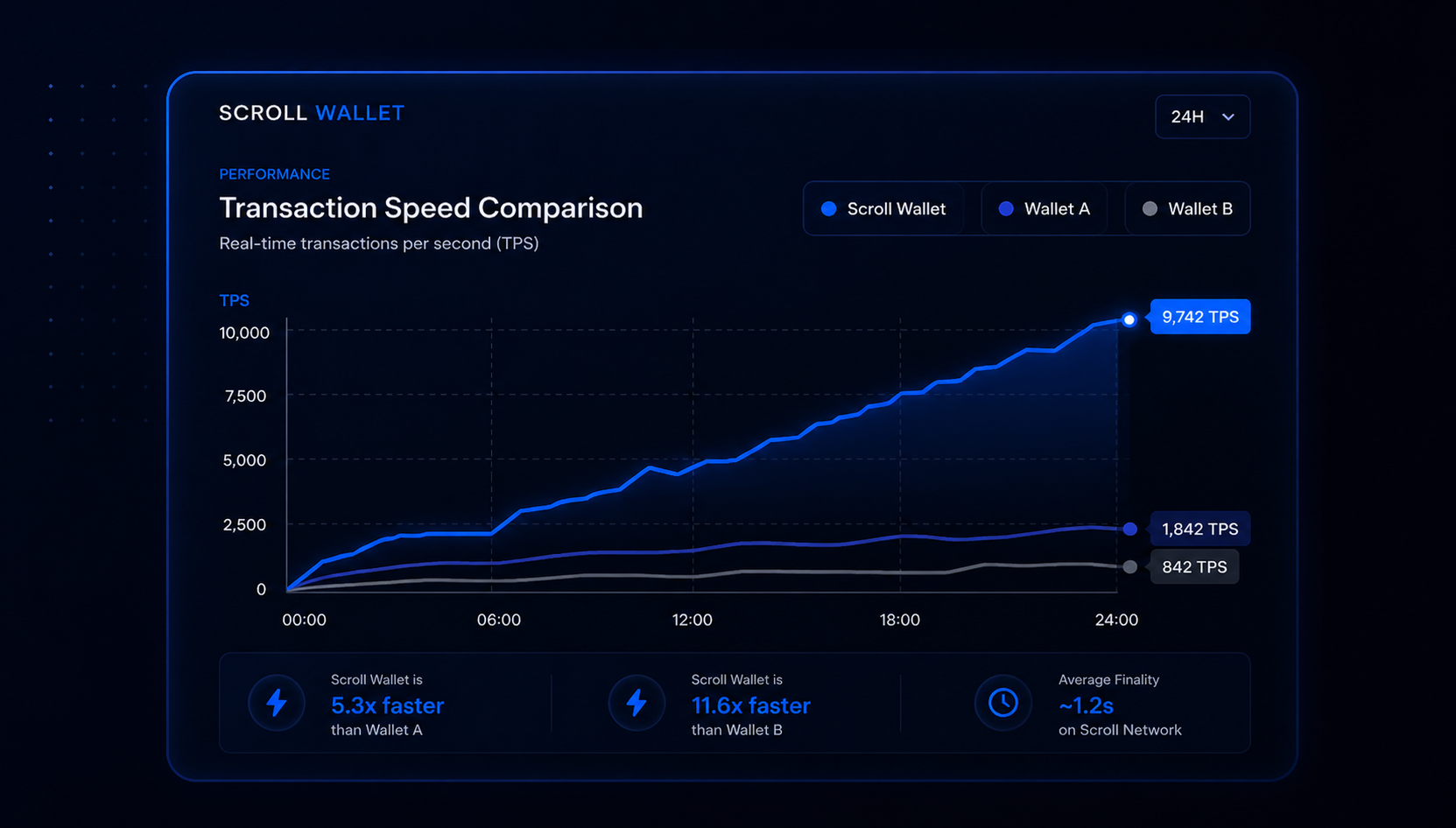
When choosing a safe private payment solution, you must evaluate the trade-offs between transaction speed, network fees, and the risk of third-party intervention. Traditional banking and centralized apps often impose high withdrawal friction and freeze risks, whereas decentralized Layer 2 solutions like Scroll Wallet provide superior privacy control and near-instant settlement with minimal costs.
| Receiving Method | Average Fees | Settlement Speed | Freeze Risk | Privacy Control |
|---|---|---|---|---|
| L2 Stablecoins (Scroll) | ~$0.01 | <1 second | Minimal | Superior (Self-Custody) |
| Private CBDCs | 0.1% – 1% | Instant | Low (Decentralized) | High |
| Tokenized Deposits | 0.5% – 2% | 1 – 5 seconds | Moderate | Medium |
| Bank Transfers | 1% – 3% | 1 – 3 days | High | Low |
Achieving a higher level of privacy when receiving digital assets requires a systematic approach to technical setup and data management. By following these steps, you can minimize the link between your real-world identity and your on-chain activity within the Scroll Wallet ecosystem.
On-chain traceability isn't a future problem — it's the structural fault line running through digital payments right now, and better architecture is the only real fix. Public ledgers keep getting sharper. Blockchain analytics tools are now standard kit for compliance teams. And the gap between what users actually need from financial privacy infrastructure and what most wallets deliver? It keeps widening. The question was never whether privacy matters in digital payments. The question is which infrastructure is built to handle it — honestly, responsibly, at scale.
The Bank for International Settlements put it plainly in recent research: the financial system is actively moving toward privacy-enhancing technologies and more advanced payment architectures. Not a fringe take. Not a crypto-native talking point. Institutional recognition, published and sourced, that transaction-level exposure creates real risk for individuals and businesses alike. Product teams building in this space have watched it firsthand — users need systems where privacy is a design principle baked into the foundation, not a layer someone bolted on after the fact. That distinction separates infrastructure built for where we're heading from wallets that made sense in a simpler, earlier on-chain world.
The adoption curve is accelerating. But it's brutally uneven. Most users still run on general-purpose wallets that expose full transaction histories by default — no meaningful controls, no real limits on what counterparties or third-party trackers can observe. Architecture decisions start mattering a lot here. Scroll Wallet is built on a single hard premise: privacy control belongs at the infrastructure level, not delegated to users through manual steps that require technical fluency most people don't have. Use a wallet that treats privacy as a core feature rather than an afterthought, and you reduce exposure without needing to become an expert to manage it. Simple. Structural. Deliberate.
The wallets that stay relevant won't be the loudest ones. They'll be the ones combining verifiable architecture with clear UX and honest risk communication — real controls, transparent trade-offs, systems you can actually verify. As multi-chain and L2 environments grow more complex, the infrastructure layer becomes the deciding factor. Not the marketing copy. Not the claims. The architecture. Scroll Wallet is built around that reality: privacy as a structural property, not a positioning exercise.
The risks of receiving money anonymously are real, layered, and brutally underestimated — and knowing them before you move is the only thing standing between you and serious financial damage. Peer-to-peer transfers, unverified wallets, privacy-focused payment channels — each one carries its own failure points, and they are not small. Scams targeting anonymous recipients thrive precisely because reversals become nearly impossible once funds flow through privacy-preserving infrastructure. You receive funds from an unknown party with zero on-chain identity attached. Then what? If the transaction turns out to be fraudulent, your recourse is essentially nothing.
Payment privacy risks stretch far beyond scams, though. Account freezes are a documented, real-world consequence of receiving funds that trip automated compliance flags — even when you have done absolutely nothing wrong. Centralized exchanges and custodial wallets freeze balances routinely when inbound transactions match patterns linked to unverified sources or high-risk jurisdictions. As Stripe points out in its breakdown of anonymous payment methods, the operational and fraud-related tradeoffs are significant for businesses and individual users alike: anonymous inflows create audit gaps that expose accounts to sudden restriction, with little warning and almost no meaningful appeal path. Once your balance is frozen, proving the legitimacy of funds received without identity metadata is a nightmare — and often a losing battle.
Then there is the liquidity trap. Funds received through privacy channels may be technically accessible on-chain but practically dead weight if no compliant off-ramp will touch them. You hold a balance you cannot convert, spend, or move without triggering fresh scrutiny. No dispute mechanism. No chargeback. No third party to escalate to. If a smart contract behaves unexpectedly or a fiat leg of a hybrid transaction gets reversed, on-chain evidence is your only card — and in a legal or platform context, that card is often not enough. Our ZK rollup privacy guide goes deep on how zero-knowledge architecture shapes these tradeoffs at the protocol level, including which privacy guarantees are actually verifiable and which ones you are simply trusting exist.
Scroll Wallet approaches this differently. The architecture separates what is visible on-chain from what compliance operationally requires — so you are not forced into an impossible choice between privacy and usability. That said, no system makes these risks disappear. Scams, freezes, liquidity gaps, weak recourse — they live at the intersection of protocol design, platform policy, and counterparty behavior. Understanding precisely where each risk originates is not optional. It is the only way to manage them with real precision instead of wishful thinking.

Scroll Wallet for private payments hands you direct control over who sees your transaction data, how funds move, and exactly what on-chain footprint you leave behind. Custodial services hold your keys and log everything. Scroll Wallet doesn't. It runs on a self-custody model built on the Scroll L2 network — an EVM-compatible zkEVM rollup that processes transactions with zero-knowledge proofs. Your payment activity gets verified on-chain without broadcasting the full details of every interaction to third parties by default. You own the keys. You authorize each transaction. No intermediary can freeze or redirect your funds.
The cost advantage hits just as hard. Scroll is a Layer 2 network, which means gas fees are a fraction of what Ethereum mainnet charges — often under $0.01 per transaction under normal conditions. For anyone receiving regular payments or juggling multiple incoming transfers, that gap compounds fast. Lower fees mean you keep more of what actually lands in your wallet, and smaller, more frequent payments stop being financially absurd. Researchers at the Bank for International Settlements (BIS) have confirmed that zero-knowledge proof systems provide a technically sound foundation for privacy-preserving transaction verification — the exact design principle that shapes how Scroll's zkEVM handles data minimization at the protocol level.
Scroll Wallet also closes a gap that most payment tools quietly ignore: receiving funds without bowing to a platform's permission system. With a self-custody wallet on Scroll, you generate your own receiving address, share it on your terms, and collect funds directly — no exchange routing, no payment processor imposing limits, delays, or identity requirements. In 2026, where multi-chain environments and bridge fragmentation have made clean payment flows genuinely difficult, this matters. Scroll's EVM compatibility lets you receive assets from any EVM-compatible chain with minimal friction, while your funds stay under your direct control at all times.
The trade-offs deserve straight talk. Self-custody means full responsibility — lose your seed phrase and there is no recovery path, no support ticket, no safety net. Scroll Wallet offers no insurance, no reversals, no account recovery team. The privacy protections baked into the zkEVM architecture reduce on-chain data exposure, but they do not render transactions invisible to every possible observer, and they are not a substitute for solid operational security on your end. What Scroll Wallet delivers is a technically grounded, low-cost, self-sovereign environment for receiving and managing payments — one where control stays with you, not with a platform that can change its rules overnight.
Privacy in crypto is structural — it lives in the tools you pick, the habits you build, and the data you refuse to hand over at every single step. No method wipes the slate clean. Every on-chain transaction leaves a permanent record. Every KYC exchange welds your identity to an address the moment you sign up. The realistic goal here is not to vanish — it is to stop leaking data you never needed to share in the first place.
The failure modes are predictable and brutal. Reusing wallet addresses collapses your privacy across every transaction you have ever made — one link, and the whole chain unravels. Connecting a privacy-focused wallet to a centralized exchange with identity verification? That undoes every layer of separation you carefully built. And the legal dimension is not optional. As Consumer Compliance Outlook makes clear, electronic fund transfers — digital assets included — operate inside a legal framework that demands disclosure and traceability across most jurisdictions. How you receive funds carries legal weight, not just technical weight. Pretending those limits do not exist does not make them disappear. It just makes your compliance exposure worse.
This is exactly where the architecture of a self-custody wallet stops being abstract and starts being practical. When you hold your own keys, no third party sits between you and your incoming funds, logging activity or tying your identity to your balance. Scroll Wallet is built on that principle. Payments arrive directly to an address you control — no custodian watching, no institution reporting. Compare that to a bank transfer or a custodial crypto account, where every incoming payment gets recorded and often flagged. The gap is real. The trade-off is equally real: self-custody puts security entirely on your shoulders. Key storage, phishing resistance, address hygiene — all yours to manage.
Operational discipline is what separates people who actually reduce their data footprint from people who just think they do. Using Scroll Wallet on the Scroll L2 network delivers lower fees and faster settlement — but more importantly, it puts distance between your activity and high-traffic chains where address clustering is trivially easy to perform. Fresh address for each payment context. No mixing of sources. A clear-eyed understanding of exactly which steps in your flow legally require identity disclosure. That combination — the right tool plus the right behavior — is what privacy in 2026 actually looks like. Not a magic shield. A disciplined reduction of unnecessary exposure, one transaction at a time.